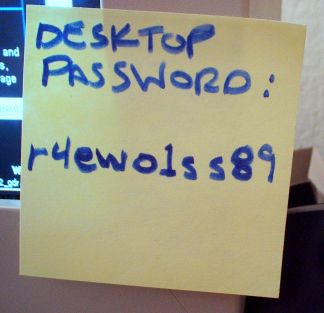
I’ve been doing a lot of thinking about passwords recently. Be honest – how many of your employees’ desks have login information on a Post-It note taped to them right now?
In my experience, probably most.
Passwords seem pretty mundane on their face, but they are fascinating, revealing, incredibly dangerous pieces of information. How many things that we hold dear sit behind passwords? The obvious: bank accounts, email services, social media. The everyday: entertainment from Netflix, your Android or iOS appstore, a voicemail PIN, a security code at the office. The priceless: Flickr accounts full of photos of your family. Forums where you have a good reputation, or worst of all: accounts that give access to other accounts (i.e. Facebook,Google, or Apple passwords that allow sign-in to other services).
So we rely of these strings of characters for quite a bit.
Unfortunately, they are not particularly safe.
Kill the Password
A lot of this began when I read Mat Honan’s wonderful and frightening article “Kill the Password: Why a String of Characters Can’t Protect Us Anymore” from Wired, where he is a senior writer. Wired is a technology print and web magazine that thrives on the bleeding edge of technology and science. Wired’s readers are plugged-in, early adopting technophiles and accordingly, their writers are some of the most “in-the-know” tech folks you’ll find.
But even access to the latest gadgets, thinkers and perspectives couldn’t protect Mat’s passwords.
This summer, hackers destroyed my entire digital life in the span of an hour. My Apple, Twitter, and Gmail passwords were all robust—seven, 10, and 19 characters, respectively, all alphanumeric, some with symbols thrown in as well—but the three accounts were linked, so once the hackers had conned their way into one, they had them all. They really just wanted my Twitter handle: @mat. As a three-letter username, it’s considered prestigious. And to delay me from getting it back, they used my Apple account to wipe every one of my devices, my iPhone and iPad and MacBook, deleting all my messages and documents and every picture I’d ever taken of my 18-month-old daughter.
Scary right?
Mr. Honan goes on to argue that the problem is passwords themselves. That regardless of how long or complex the password, it can eventually be cracked by technical, sociological, or subversive means. No password is sincerely safe, only protected by the amount of effort it would take to break it. If someone wants to break in, it is really only a matter of time.
How does this relate to HIPAA?
There is a compliance component to all of this as well. Password management has to be a part of your HIPAA compliance plan. Those passwords also protect your PM and EMR systems, and all that precious Protected Health Information they contain. Let’s take a look at the Administrative Safeguards section of the HIPAA Security Rule.
4. PASSWORD MANAGEMENT – § 164.308(a)(5)(ii)(D)
The last addressable specification in this standard is Password Management. Where this
implementation specification is a reasonable and appropriate safeguard for a covered entity, the covered entity must implement:“Procedures for creating, changing, and safeguarding passwords.”
In addition to providing a password for access, entities must ensure that workforce
members are trained on how to safeguard the information. Covered entities must train all
users and establish guidelines for creating passwords and changing them during periodic
change cycles.Sample questions for covered entities to consider:
Are there policies in place that prevent workforce members from sharing
passwords with others?Is the workforce advised to commit their passwords to memory?
Are common sense precautions taken, such as not writing passwords down
and leaving them in areas that are visible or accessible to others?
So while HHS does not mandate a specific plan, it does mandate that a plan is in place. Thankfully Mat Honan has a bunch of suggestions in his article, but here are four of his “DON’T“s that you could bring up in your next staff meeting while discussing your new password policy.
- DON’T Reuse passwords. If you do, a hacker who gets just one of your accounts will own them all. (Some systems will not let you reuse passwords.)
- DON’T Use a dictionary word as your password. If you must, then string several together into a pass phrase.
- DON’T Use standard number substitutions. Think “P455w0rd” is a good password? N0p3! Cracking tools now have those built in.
- DON’T Use a short password—no matter how weird. Today’s processing speeds mean that even passwords like “h6!r$q” are quickly crackable. Your best defense is the longest possible password.
Now, why don’t you go change some of your passwords right now?